Account Data Review – 185.63.253.290, 8554637258, Ofillmyzilla .Com, englishrebecca26xxx, 8334100241
The data points present a fragmented digital footprint bound to specific identifiers. The account data review should proceed with caution, emphasizing provenance, cross-reference integrity, and privacy safeguards. Methodical skepticism is warranted to avoid duplication and exposure while acknowledging limits in correlation. The consequences for individuals and brands are nontrivial, demanding strict hygiene and verifiable audits. The discussion will hinge on how to tighten controls, yet important uncertainties remain, inviting continued examination of practical safeguards and residual risks.
What the Data Points Reveal About Online Footprints
The data points collectively map a digital footprint that is both fragmented and informatively bounded, revealing patterns of online activity tied to specific identifiers without implying broader, unverified conclusions.
The analysis remains cautious, highlighting privacy risks and the need for disciplined data hygiene.
Conclusions are provisional, emphasizing verification, context, and the limitations of inferred behavior within a free, skeptical framework.
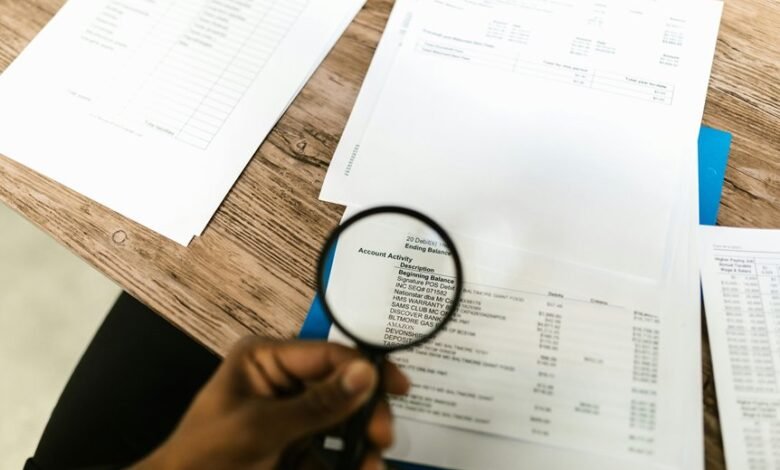
How Identifiers Are Collected, Linked, and Analyzed
How identifiers are collected, linked, and analyzed hinges on a disciplined, multi-step process that emphasizes provenance, correlation limits, and privacy safeguards. The methodology catalogs sources, cross-referencing signals while enforcing data hygiene to minimize duplication and error. Analysts remain skeptical, questioning assumed connections and potential leakage. Privacy risks are acknowledged, yet practical governance must balance insight with user autonomy and transparent accountability.
Risks and Implications of Exposure for Individuals and Brands
Exposure of sensitive identifiers can precipitate a cascade of negative outcomes for both individuals and organizations. A careful risk lens reveals distorted privacy as a pivot, amplifying data misuse, targeted exploitation, and unequal protection.
For brands, exposure compounds reputational risk, eroding trust, investor confidence, and platform integrity.
For individuals, consequences include financial loss, credential theft, and long-term credentialing barriers; mitigation requires deliberate controls and vigilant monitoring.
Practical Steps to Improve Data Hygiene and Privacy Controls
Practical steps to improve data hygiene and privacy controls demand a structured, evidence-based approach that peer reviews its own effectiveness. The method evaluates privacy safeguards, enforces data minimization, and strengthens data governance without bias.
Clear policies on user consent, verifiable audits, and ongoing risk assessment enable accountable freedom, while skeptical scrutiny ensures implementations remain proportionate, transparent, and continuously improvable.
Frequently Asked Questions
How Often Should Individuals Audit Their Own Online Identifiers?
Auditors should conduct the review annually, with ad hoc checks during policy changes; the process emphasizes audit frequency balanced against data minimization. The disciplined observer questions necessity, maintains skepticism, and favors freedom through purposeful data minimization.
Do Data Exposures Affect Credit Scores or Loan Offers?
Data breach impacts can ripple through credit score implications, but not instantly; credit reports reflect ongoing risk, while lenders assess income, utilization, and history. The meticulous observer notes no automatic doom—alerts and corrective steps matter. Skeptical transparency wins.
Can Family Members’ Data Be Linked to a Compromised Account?
Families’ data can be linked to a compromised account, but only through targeted, uncommon correlations; privacy safeguards and data sharing policies determine risk, demanding skepticism and rigorous verification before conclusions about family linkage are drawn.
What Legal Protections Apply to Exposed Personal Identifiers?
Exposed personal identifiers trigger data privacy basics concerns; legal remedies for exposure vary by jurisdiction. The analysis demands caution, skepticism, and insistence on transparent accountability, aligning with freedom-focused audiences who expect robust privacy protections and enforceable remedies.
How Long Do Data Brokers Retain Collected Identifiers?
Data broker retention varies; no universal standard exists. The identifier lifecycle spans collection, normalization, enrichment, and eventual deletion or anonymization, often driven by policy, legislative pressure, and market demand, while safeguarding individuals’ freedom through transparency and accountability.
Conclusion
In summary, the data review presents a methodical, skeptical appraisal of the exposed identifiers, tracing potential linkage while acknowledging gaps and uncertainty. The analysis treats correlations as provisional, avoiding overreach and highlighting exposure risks for individuals and brands. While patterns emerge, confidence remains tempered by incomplete provenance and leakage possibilities. Practitioners should proceed with caution, implementing rigorous hygiene and audits. Bottom line: proceed with caution, and keep a tight lid on data sharing to avoid fanning the flames.





